Best Ways to Protect Against Email Phishing
Protecting against email phishing attacks continues to be a top priority for cybersecurity teams. Email phishing is significantly rising and becoming even more dangerous. Attackers integrate behavioral intelligence with social engineering tactics in building trust with users. Moreover, these tactics allow attackers to easily infiltrate devices and critical IT systems.
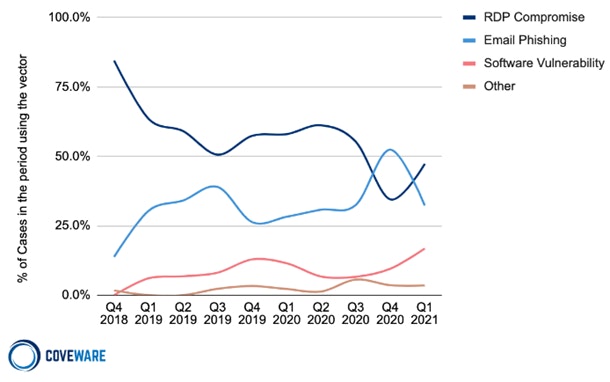
Email phishing is a specific type of social engineering attack involving fraudulent emails delivering malware or attempting to coerce the recipient into disclosing sensitive information. Phishing has consistently been a primary attack vector for ransomware. According to a 2021 study by Coveware, email phishing was the second most common initial attack vector with around 30 to 40% of all ransomware attacks coming through email phishing. Phishing is a threat that just won’t go away because it targets humans, the weakest part of any IT security plan. Hackers will always attempt to gain access through social engineering as it is a much more consistent vulnerability across businesses and governments around the world. With that in mind let's discuss what email phishing looks like and how to protect yourself from them.

Real World Email Phishing Example
Here is a real-world example of a phishing email provided by the Federal Trade Commission, the regulatory body that investigates phishing and other forms of fraud. Even though this may appear to be a trustworthy email, in reality, it proves the increasing effectiveness and continuing evolution of email phishing.
This type of deception continues to become more common, and can even be hand-crafted to spear phish a specific person. Any email containing a call to action requesting a user to click a link, especially if it involves resetting your password, should be highly scrutinized. A good rule for emails like these is to avoid clicking any links and to instead reach the specific web page independently. For this example, instead of clicking the email link, we recommend going to Netflix’s website directly and navigate to your account’s payment settings. If the email is legitimate, a notification on your Netflix account would prompt you to update your account. In short, this avoids the potentially dangerous link while still allowing you to update your payment information if needed.
How to Protect Yourself from Attacks
We previously discussed the importance of avoiding interacting with email links. In addition, other tactics exist to protect yourself and your organization from email phishing attacks and ransomware. Furthermore, to effectively provide protection from phishing attacks, update your IT security plan to include the following:
- Update staff training including best practices to avoid email phishing. It is of the upmost importance this training is continuously updated to cover new social engineering developments as they occur.
- Security software including network monitoring solutions, antivirus software, and email quarantine solutions for suspicious emails.
- Automatic or consistent system updates. These updates patch out security vulnerabilities and offer a natural security barrier against attackers.
- Enable multi-factor authentication for access to the network or any programs that involve mission critical data. This provides an additional layer of security preventing a ransomware attack from succeeding.
- Develop a robust backup and recovery system. In the event of a successful ransomware attack, a backup and recovery system is your last line of defense. It allows you to restore your data and prevent paying a costly ransom. This also minimizes downtime and allows you to quickly recover if an attack does occur.
- Invest in a Security Information and Event Management Platform (SIEM). A great compliment to you Security Operations Center (SOC) or Network Operations Center (NOC) is a quality SIEM platform. SIEMs enable your IT team to automate tedious tasks, updating and archiving event logs, and create workflows for specific events. Furthermore, SIEMs help IT to easily establish remediation protocols, and monitor behavioral trends of users.
Contact Strategic Communications for More Inforamtion
Phishing is an incredibly important security threat that all organizations must consider in their IT security plans. With the proliferation of ransomware in recent years, it has become an even more dangerous attack vector. To learn more about how to protect yourself from Email Phishing attacks and ransomware click the button below to talk to a cyber security expert at Strategic Communications.



